Hi there kids, welcome to networking club. Here are the rules:
- Don’t talk about fight club.
Annnnd that’s it. Ok, let’s get started then. So you realized you don’t know how dem old internet tube highways things actually work, and you thought you would get some learnings. You have come to the right place.
This post assumes you know basic things about IP addresses. If you don’t, well, this is going to be confusing.
In this first lesson, I want to start simple. I just want to explain what actually happens when two computers on the same network send each other messages.
Suppose I have two computers, A and B.
A: 192.168.0.10
B: 192.168.0.11
Make sure you take note of these numbers closely, because as it turns out I never actually reference these numbers later on and they are useless. Got it? Great.
Let’s suppose A and B are connected to the same switch, and nothing else is connected to the switch. When A sends a packet to B, what happens?
WRONG! Oh, you didn’t actually answer? Well… you are still wrong. Here is what happens:
It sends the packet. Duh. You should know that part already.
But as it turns out, it isn’t actually that simple. There is a hidden layer underneath that you probably haven’t touched before.
Layers
When computer A wants to send a packet to computer B, it first must check its ARP cache for computer B’s IP address.
ARP cache? What de heck is an ARP cache?
I was just getting to that. So, the first thing most people learn about computers networks is that all computers have an IP address, and that is how they send packets to each other.
Now as it turns out, there are multiple layers of protocols. And, because humans are so creative, we gave each of them a number. Layer 1, the lowest level, is basically just the electrical part, where all the fancy bits go in the fancy cable and woop de do they end up on the other side. I don’t know how any of that stuff works, so let’s skip that.
After layer 1 is… dun dun dun… layer 2. Layer 2 is technically called the data link layer, or something fancy like that, but practically speaking it is just the “Ethernet protocol.” Layer 2 actually has its own type of addresses: MAC addresses. You may have encountered these before. They look like this:
2A-51-1F-2A-F9-DE
Anything that has an IP address also has a MAC address. If you run ipconfig /all on windows, it is listed as the Physical Address for a given interface.
After layer 2, naturally, is layer 3. Layer 3 is the network layer. You can think of it as the IP layer. So you have layer 2 addresses – MAC addresses – and you have layer 3 addresses – IP addresses. Every packet on the network has a layer 2 and layer 3 component.
The layer 3 part is contained inside the layer 2 part. If you read a networking textbook, they have fancy diagrams explaining this concept, which is called encapsulation. But we aren’t fancy here, so I will make it simple. Let’s say you have a box. Then, because you do like boxes so good, you put that box in a bigger box. Oh, and also, you wrapped both of them in wrapping paper, because it is shiny.
In other words, you encapsulated a box inside another box. Now, suppose somebody sent you a similar box, which has an outer box and an inner box. And maybe you think of yourself as an outer box guy, and your friend is the inner box guy. So the outer box comes to you, you unwrap it, then you pass the inner box to your friend, who then opens it and finds what is on the inside. In this example, you, the outer box guy, are acting as layer 2. Your friend is layer 3.
Let’s use another example. Suppose you went to google.com. Let’s say that is the innermost contents of the box. Then, you wrap that up in a box that has google’s IP address on it, so it ends up in the right place. That is, you put on the layer 3 wrapping. Then, you put that box in another box, and label that outer box with the MAC address of your destination – this is the layer 2 wrapping. You feel very accomplished, and send your box to the destination.
When your box arrives at the destination, this entire process happens in reverse. When you sent the box, you had the packet contents (google.com, for example – we can call this the application layer), then the network layer was added onto it, and then the data link/ethernet layer – layer 2 – was added onto that. So, when the destination end unwraps the box, they first see layer 2, and then layer 3, and then inside it all is whatever you sent to google.com.
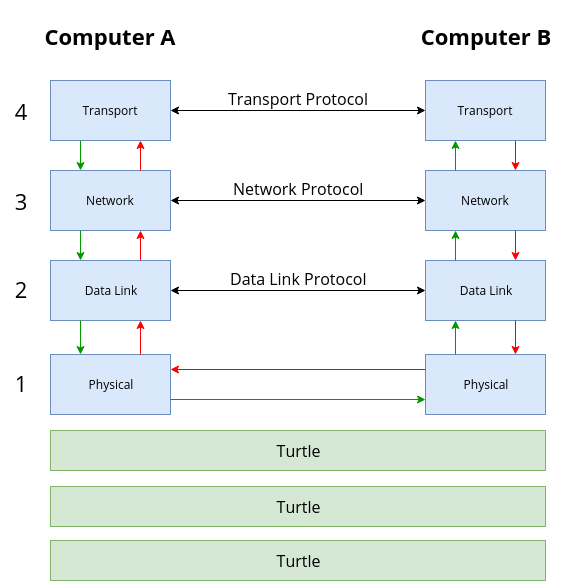
Earlier, when I said I wasn’t fancy? I lied. I am super fancy, and I made this picture with a bunch of rectangles just for you. As you can see, when Computer A sends a packet, it starts at the highest layer – in this case, transport – and makes its way down the green arrow path, adding more and more layer wrappings, until it reaches the physical layer. There are also a bunch of turtles below there – turtles all the way down, as it turns out – but we can ignore those.
So the packet goes down to the physical layer. It then goes across the network in a cable, or perhaps calls for a cab. Then, it reaches the other computer at the physical layer, and works its way all the way up to the transport layer on the other side, shedding layers as it goes up.
When computer B sends a reply packet, that entire process happens in reverse. The packet goes down the stack on computer B, adding each successive layer, and it then is transmitted on the physical layer. Upon reaching computer A, each layer is peeled back, and the inner box is passed up to its respective layer.
As indicated by the fancy black lines in the middle, each layer, in a way, only communicates with its direct neighbor. Generally speaking, no protocol knows anything about the layer above it, and for the most part doesn’t care what is below it.
For common TCP/IP networks, Layer 2 is Ethernet, Layer 3 is IP, and Layer 4 is TCP (or UDP).
The “box” at each layer in this diagram, and the data it contains, has a specific name. There is a generic name, Protocol Data Unit (PDU), that is often used for the higher layers. But the lower layers have special names because they are referenced often. The outermost box with layer 2 information is called a frame. The inner box, with layer 3 information, is called a packet. They basically mean the same thing, but reference which step/layer we are looking at.
So that explains what layers are. The remaining question is, what is the ARP cache, and why is it needed to sent packets?
ARP
ARP is Address Resolution Protocol. It is used to map IP addresses to MAC addresses, and vice versa.
When computer A wants to send a packet to computer B, it has to prepare the boxes – layers – we mentioned before, so it can be “shipped” across the network. In this case, that means we need a layer 3 box as well as a layer 2 box. So computer A not only needs the IP address of computer B, which we already have (layer 3), but also the MAC address of computer B (layer 2). We cannot send computer B a packet (box) until we get its MAC address. This is where ARP comes in.
As I mentioned, everything with an IP address also has a MAC address. But how do you know which IP address corresponds with which MAC address, and vice versa? ARP to the rescue!
ARP is a layer 2 protocol. Most protocols you use, like HTTP (websites), are pretty high on the protocol stack (network layer stack), involving at least four layers of network protocols. But some protocols only exist at lower levels of the protocol stack, and ARP is one of them. So ARP, being at layer 2, exists below the IP layer (layer 3).
That means that when we send boxes for ARP, they only contain layer 2 stuff, not layer 3 stuff. It would be like if sending mail to somebody in the same city didn’t require a zip code. Because the path between the sender and recipient is simple (two computers on the same local network), less information (layer 3 box) is needed to get the box from A to B. So, ARP messages only need to be wrapped in a frame and not a packet.
Also, with Ethernet (layer 2), there is a special MAC address used for broadcasts, FF-FF-FF-FF-FF-FF. That’s a lot of F’s, my friends.
When we send layer 2 frames – just like packets, but at layer 2 – to this broadcast address, they actually go to every computer on our layer 2 network. This basically means every computer in your house.
So when your computer is trying to find the MAC address of another computer it has the IP of, it sends out an ARP discovery message to the entire network, asking “Who is using IP 192.168.0.11? Please respond to me, I am so lonely.”
Because that is sent to the broadcast MAC address, all computers on your network get it. One of the computer that gets it is computer B. Computer B looks at it and says “hm… I think that is my IP”, and having realized that, it replies to computer A and says “sup”.
When computer A sent the broadcast message, the source MAC address was also included – like a return mailing address. So when computer B received the message, it also received the MAC address of computer A, which allows it to send an answer directly back to computer A. The answer computer B sends to computer B is basically “I am using that IP address.”
And once A receives that frame from computer B, it looks at the source MAC address, and it now has the MAC address associated with that IP. Computer A has learned the MAC address of computer B.
So in the bigger picture, computer A wanted to send something to computer B. But it cannot do that until it finds computer B’s MAC address, so it sends out an ARP message. Computer B responds to that message. Now computer A, armed with computer B’s IP and MAC address, has all the information required to send a packet (and frame) over the network.
So that is what ARP is. That just leaves the cache part.
Packets get sent all the time on most networks. If computers had to send ARP requests every single time they sent a packet, it would double the traffic on the network, which is no good. So instead of doing that, computers remember MAC addresses they have learned through ARP in the ARP cache. In windows you can view this with the arp -a command, which shows (a)ll entries your computer has learned.
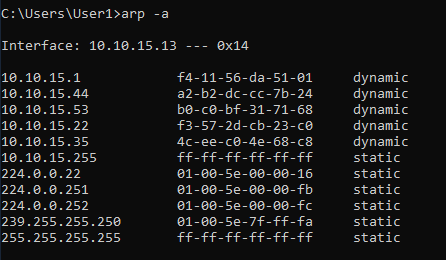
This is just like DNS caching. Entries in the ARP cache are only stored for a bit – as short as a minute – before they “fall out” of the cache and an ARP request has to be performed again. The reason for this is that if a computer’s IP address changes and a different computer gets that same IP address, then traffic intended for the first computer would end up going to the second since the ARP cache stores things by IP address. So it is stored long enough to prevent needing to send ARP packets all the time, but also refreshed often enough to not cause connectivity problems.
Conclusion
What did we learn today?
Um… a^2 + b^2 = c^2?
Kids these days….
In theory, you learned two things. First, computer networking involves layers of protocols, and layer 3 is the network (IP) layer and layer 2 is the data link (Ethernet/MAC address) layer. Every packet on the network contains both of these things.
Second, ARP is the protocol which binds these two layers together, by enabling computers to find MAC addresses based on an IP address.
Understanding that networking works in layers might not seem important at first, but as it turns out, most higher-level networking is just adding more layers on, and understanding how these layers interact with each other and what each layer does makes it much easier to troubleshoot when things go wrong.
consists of the book itself
Marketing your home for money and revolving properties for profit can be an excellent method to create revenue in the property sector, but it requires thorough organization and preparation. Start by correctly evaluating your home’s market value, which you can attain through licensed assessments, comparisons with comparable properties, or online valuation resources. Correct pricing is essential to prevent monetary losses or prolonged offering times. Engaging a housing agent can offer important advice to aid you determine a fair and realistic price matching existing marketplace trends.
Prior to listing your home for cash, emphasize on performing essential improvements and improvements, especially in important sections like the cooking area and restrooms, which can substantially enhance your house’s worth and attractiveness. Verifying that your home is tidy and clean is important to luring prospective investors quickly. Additionally, preparing your property by tidying up, placing furnishings strategically, and introducing tasteful decorations can create an welcoming environment that increases buyer attraction. Engaging a certified home arranger can additionally enhance your home’s presentation.
For those aiming to flip properties for gain, securing the suitable funding is vital. Choices such as conventional bank credits, hard money credits, and private credits are obtainable, and it’s critical to select one that fits with your monetary situation and project requirements. Ensure you have a robust return approach in place. Collaborating with the appropriate experts, like real estate brokers, renovators, assessors, and legal professionals, is vital for a effective house renovating venture. These professionals can assist in discovering the best home, conducting renovations, examining estate status, and overseeing legal matters, securing a seamless and lucrative renovating procedure. For additional details and references on this topic, feel free to visit my top site.
Should you wanna study more info on your matter take a look at my own web site:
quick
How We Help Georgia Homeowners Avoid Foreclosure 79e459a
Eye Movement Desensitization and Reprocessing (EMDR) is a clinically supported therapeutic approach that is often discussed in relation to stress-related experiences.
This method focuses on helping the brain process stored information in a systematic way. By using two-sided processing, EMDR supports the brain’s natural processing capacity.
Rather than relying entirely on verbal recounting, this method emphasizes internal processing within a client-centered environment.
Within professional settings, EMDR is often described as part of a broader trauma-informed care model. Ongoing research continues to reference EMDR in discussions of recovery-oriented care.
Tips to Find a Great Eye Movement Desensitization and Reprocessing Practitioner for Your Unique Healing Journey 1_f7465
Photography enables a way to preserve authentic emotion beyond what written descriptions fully explain. Every captured image reflects intent through light. Instead of focusing on forced expression, creative photography highlights authentic interaction. From celebrations to quiet scenes, photography remains a creative archive of experiences worth remembering.
Preserving Love Seattle Wedding Imagery Narrative Through Nuptial Imagery aa754ad
Picking the appropriate components for a project plays a major role in how the final result holds up. The materials you select directly affect longevity and visual appeal. Multiple materials offer varied advantages, with some being better suited for outdoor conditions and others performing best in protected environments. Thinking about factors like usage and cost helps ensure the finished work is both reliable and well-balanced.
Investigating the environmentally friendly advantages of using real stones. dc80_c1
Dessert decorating activities are becoming a enjoyable choice for participants to interact in a relaxed environment. Unlike standard team events, decorating cakes allow people to share ideas while creating something visual. These creative experiences are commonly chosen for team bonding, celebrations, and small group programs. Participants can explore basic decorating techniques while enjoying a supportive atmosphere. Because everyone gets involved, these activities naturally support teamwork. Whether the goal is group engagement, creative baking provides a enjoyable experience that works well for many types of groups.
Indoor vs. Outdoor Team Building Activities in South Florida: Which Is Better for Your Company? fe49e57
What seeking assistance from the government long-term disability attorney.
The government benefits office oversees SSI programs for those who are not able to perform substantial work due to illness.
Because the system requires specific rules, filings must be filed carefully to avoid issues.
Retaining an knowledgeable Social Security counsel may assist you handle the process, gather medical history, and fulfill deadlines.
If a claim is denied, they can also prepare you for an further proceeding, maximizing the potential of a approved outcome.
Why You Should Have an Counsel Experienced in Disability Matters on Your Team d8dc81_
A secure safe offers more than basic protection. Features like heavy-duty construction, digital locks, and fire-resistant materials help keep valuables protected in unexpected situations. Using the right safe helps ensure important items remain secure whether at home.
Comprehending Biometric Safes: Cutting-edge Protection in Scottsdale area 9afe49e
Offering your property for money can be a straightforward way to free up funds. To start, get a clear idea the likely price of your property by reviewing comparable sales and factoring in the condition. Next, price it reasonably so it doesn’t sit too long. If time matters, local investors may buy as-is. Keep it simple: do basic cleaning, prepare details like timeline, and be upfront about any issues. With a solid approach, you can reduce stress and get to the finish line.
What to Do When You Need to Sell a House That Needs Repairs c81_cd2
Hello colleagues
Hi. A 32 cool website 1 that I found on the Internet.
Check out this site. There’s a great article there. https://jmnoticia.com.br/kaka-pensa-em-virar-tecnico/|
There is sure to be a lot of useful and interesting information for you here.
You’ll find everything you need and more. Feel free to follow the link below.